原文地址:http://chezw.blog.51cto.com/67821/134572
下面在Cisco交换机上实现简单的端口绑定,举Cisco 3550为例:
//进入通用配置模式
3550(config)# Interface fastethernet 0/1
//进入需要配置的具体端口配置模式
3550(config-if)#switchport mode access
//设置交换机的端口模式为access模式,注意缺省是dynamic
//dynamic模式下是不能使用Port-security功能的
3550(config-if)#switchport port-secruity
//启用端口安全模式
3550(config-if )switchport port-security mac-address <后面写上主机的MAC地址>
//配置该端口要绑定的主机的MAC地址
switch(config-if)#switchport port-security maximum 1
//其实缺省就是1个
switch(config-if)#switchport port-security violation shutdown
//设置违反端口安全规则,缺省是shutdown
看看下面的配置:
3550(config)#mac access-list extended mac-n
//配置一个命名的MAC地址访问控制列表,命名为mac-n
3550(config-ext-macl)#permit host 0001.a1db.f987 any
//源MAC地址为0001.a1db.f987的主机可以访问任意主机
3550(config-ext-macl)#permit any host 0001.a1db.f987
//所有主机可以访问目的MAC地址为0001.a1db.f987的主机
3550(config)#ip access-list extended ip-n
//配置命名的IP地址访问控制列表,命名为ip-n
3550(config-ext-nacl)#permit ip 172.0.0.1 0.0.0.0 any
//允许172.0.0.1地址在网内工作
3550(config-if )#interface fa0/1
//进入配置具体端口的模式
3550(config-if )#mac access-group mac-n in
3550(config-if )#ip access-group ip-n in
2950 (config-if-range)#switchport mode Access
2950 (config-if-range)#switchport port-security
2950 (config-if-range)#switchport port-security mac-address violation restrict
2950 (config-if-range)#switchport port-security mac-address sticky
cisco(config)#arp 10.138.208.81 0000.e268.9980 ARPA
原文地址:http://blog.csdn.net/alone_map/article/details/51840512
Switch通过Arp泛红来进行MAC地址的学习,并汇聚成一张"MAC address tables",一个端口下可以有多个MAC地址的学习,因为MAC地址表的本身是有限制的,如果超过了最大定义的MAC数量,那么以后发来的MAC寻址在网络中都会进行以arp泛红的形式进行通话,这样就可以在任意的主机上抓取通信的内容,安全性得不到最大的保障。另外端口安全与arp绑定有类似的功能,灵活运用可以限制主机上网数量,总结一下端口安全配置及简单应用。
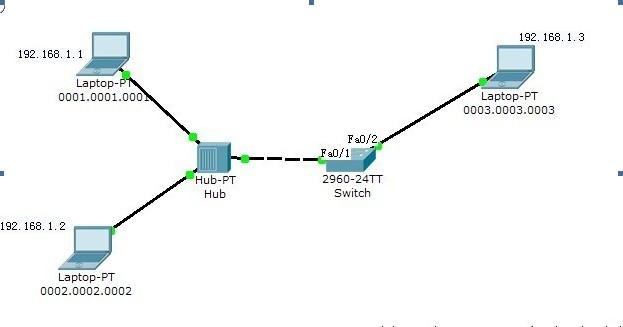
1.首先进入需要绑定的端口,比如一个端口上接一个HUB,HUB下挂了几台主机,但是只允许其中一个主
机通过该交换机的这个端口。
2.开启端口安全绑定策略
3.设置端口上允许通过的MAC地址的数量。
4.选择绑定的模式,是静态绑定(指定MAC地址,在MAC地址表中也会自动添加绑定)还是动态绑定(即
先访问此端口的MAC地址)。
5.设置端口上的安全策略,对没有被绑定的MAC地址流量想要通过此端口的处理方法,分为报警且不放行
、不报警也不放行、报警并关闭端口。
6.查看端口安全设置及,安全MAC表的设置是否正确
端口安全配置命令如下:
1.interface f0/1
2.switchport mode access
3.switchport port-security
4.switchport port-security maximun 1
5.switchport port-security mac-address [0001.0001.0001\sticky]
6.switchport port-security violation [protect\restrict\shutdown]
7.show port-security interface f0/1
8.show port-security address
完成安全端口的配置
(例如)exp1:为f0/1端口指定一个MAC地址通过,其他MAC地址想要通过时拒绝并报警,但不关闭端口
1.interface f0/1
2.switchport mode access
3.switchport port-security
4.switchport port-security maximun 1
5.switchport port-security mac-address 0001.0001.0001
6.switchport port-security violation restrict
7.show port-security interface f0/1
Port Security : Enabled 端口安全开启
Port Status : Secure-up
Violation Mode : Restrict 类型:拒绝并报警
Aging Time : 0 mins
Aging Type : Absolute
SecureStatic Address Aging : Disabled
Maximum MAC Addresses : 1 最大通过MAC地址数量
Total MAC Addresses : 1
Configured MAC Addresses : 1
Sticky MAC Addresses : 0
Last Source Address:Vlan : 0002.0002.0002:1 这里显示的是最后一次通过端口的MAC及该MAC所(用192.168.1.2ping192.168.1.3得要的)
属的vlan,本例中是0002.0002.0002 vlan1,因为策略中绑定的是0001.0001.0001这个MAC,所以显然0002.0002.0002这个MAC没有被放行通过。
Security Violation Count : 9
8.show port-security address
Secure Mac Address Table
-------------------------------------------------------------------------------
Vlan Mac Address Type (类型报警) Ports Remaining Age
(mins)
---- ----------- ---- ----- -------------
1 0001.0001.0001 SecureConfigured FastEthernet0/1 -
------------------------------------------------------------------------------
Total Addresses in System (excluding one mac per port) : 0
Max Addresses limit in System (excluding one mac per port) : 1024
以上信息也可以看出绑定的是0001.0001.0001MAC
(例如)exp2:让f0/1端口只允许一个MAC地址通过(通常是第一个访问端口的主机MAC地址),其他的一
律拒绝,如果有其他MAC企图通过时,关闭端口
1.interface f0/1
2.switchport mode access
3.switchport port-security
4.switchport port-security maximun 1
5.switchport port-security mac-address sticky
6.switchport port-security violation shutdown
7.show port-security interface f0/1
Switch#show port-security interface f0/1
Port Security : Enabled 端口安全开启
Port Status : Secure-up
Violation Mode : Shutdown 类型:拒绝并关闭端口
Aging Time : 0 mins
Aging Type : Absolute
SecureStatic Address Aging : Disabled
Maximum MAC Addresses : 1 最大允许MAC地址数量
Total MAC Addresses : 1
Configured MAC Addresses : 0
Sticky MAC Addresses : 1
Last Source Address:Vlan : 0002.0002.0002:1
Security Violation Count : 0
8.show port-security address
Secure Mac Address Table
-------------------------------------------------------------------------------
Vlan Mac Address Type (类型shutdown) Ports Remaining Age
(mins)
---- ----------- ---- ----- -------------
1 0002.0002.0002 SecureSticky FastEthernet0/1 -
------------------------------------------------------------------------------
Total Addresses in System (excluding one mac per port) : 0
Max Addresses limit in System (excluding one mac per port) : 1024
这样如果有不是MAC为0002.0002.0002的MAC要通过f0/1端口的时候,端口就会自动shutdown。查看端口状态如下
Switch#show interfaces f0/1
FastEthernet0/1 is down, line protocol is down (err-disabled) 显示因为错误而关闭(用192.168.1.1ping192.168.1.3得到的)
Hardware is Lance, address is 0060.706e.b601 (bia 0060.706e.b601)
BW 100000 Kbit, DLY 1000 usec,
reliability 255/255, txload 1/255, rxload 1/255
Encapsulation ARPA, loopback not set
Keepalive set (10 sec)
Half-duplex, 100Mb/s
input flow-control is off, output flow-control is off
ARP type: ARPA, ARP Timeout 04:00:00
Last input 00:00:08, output 00:00:05, output hang never
Last clearing of "show interface" counters never
Input queue: 0/75/0/0 (size/max/drops/flushes); Total output drops: 0
Queueing strategy: fifo
Output queue :0/40 (size/max)
5 minute input rate 0 bits/sec, 0 packets/sec
5 minute output rate 0 bits/sec, 0 packets/sec
956 packets input, 193351 bytes, 0 no buffer
Received 956 broadcasts, 0 runts, 0 giants, 0 throttles
0 input errors, 0 CRC, 0 frame, 0 overrun, 0 ignored, 0 abort
0 watchdog, 0 multicast, 0 pause input
0 input packets with dribble condition detected
2357 packets output, 263570 bytes, 0 underruns
0 output errors, 0 collisions, 10 interface resets
0 babbles, 0 late collision, 0 deferred
0 lost carrier, 0 no carrier
0 output buffer failures, 0 output buffers swapped out
Switch#show port-security interface f0/1
Port Security : Enabled
Port Status : Secure-shutdown
Violation Mode : Shutdown
Aging Time : 0 mins
Aging Type : Absolute
SecureStatic Address Aging : Disabled
Maximum MAC Addresses : 1
Total MAC Addresses : 1
Configured MAC Addresses : 0
Sticky MAC Addresses : 1
Last Source Address:Vlan : 0001.0001.0001:1 最后一次访问的MAC地址
Security Violation Count : 1
以上可以看到,通过show interface f0/1 和 show port-security interface f0/1两条命令可以看到
MAC地址为0001.0001.0001的MAC地址企图通过端口f0/1,而导致了f0/1端口关闭。在show interface
f0/1中可以看到提示信息FastEthernet0/1 is down, line protocol is down (err-disabled)。
现在用普通的方法进行端口的启用:进入f0/1执行no shutdown命令
Switch(config)#interface f0/1
Switch(config-if)#no shutdown
%LINK-5-CHANGED: Interface FastEthernet0/1, changed state to down
无法进行端口的启用,正确的启用方法为:先进性shutdown关闭,再no shutdown启用。
Switch(config)#interface f0/1
Switch(config-if)#shutdown
%LINK-5-CHANGED: Interface FastEthernet0/1, changed state to administratively down
Switch(config-if)#no shutdown
%LINK-5-CHANGED: Interface FastEthernet0/1, changed state to up
%LINEPROTO-5-UPDOWN: Line protocol on Interface FastEthernet0/1, changed state to up
Switch(config-if)#do show interface f0/1
FastEthernet0/1 is up, line protocol is up (connected)
链路及协议都up,启用成功。
方法二可以使用策略关闭的端口自动恢复,详细见端口广播风暴抑制。
命令:
L5(config)#errdisable recovery cause security-violation 为security-violation启用自动恢复
L5(config)#errdisable recovery interval 1800 恢复时间为1800s后
L5#show errdisable recovery 查看哪些策略开启了自动恢复及恢复时间
推荐本站淘宝优惠价购买喜欢的宝贝:
本文链接:https://hqyman.cn/post/1382.html 非本站原创文章欢迎转载,原创文章需保留本站地址!
休息一下~~


 微信支付宝扫一扫,打赏作者吧~
微信支付宝扫一扫,打赏作者吧~