本文详细讲解了firmadyne环境搭建及使用其进行无线路由器逆向分析的方法。
一、Firmadyne介绍
Firmadyne是一款自动化和可裁剪的嵌入式Linux系统固件分析框架。它支持系统固件逆向QEMU嵌入式系统模拟执行。使用它模拟路由器固件执行路由器,然后可以基于模拟环境进行路由器漏洞挖掘、渗透攻防。
Firmadyne是当前最先进的固件仿真框架,很多研究都用其进行动态分析。
Firmadyne在解包固件映像后使用预先构建的定制Linux内核和库来模拟它。这些内核和库是预先构建的,以支持各种硬件功能,如NVRAM。 Firmadyne模拟目标映像两次:
第一次模拟记录有用的信息。
第二次模拟利用记录的信息。
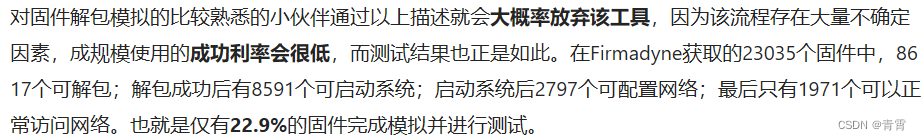
仿真过程简单、仿真速度快,缺点就是仿真成功率低。主要是因为固件品牌的高度定制化和固件的异构性。
它 包含以下组件:
一个固件提取器(
extractor ), 用于提取嵌入式firmware固件的filesystem 和kernel;
一个
scraper ,用于下载 firmware固件(从 42+ 不同供应商).
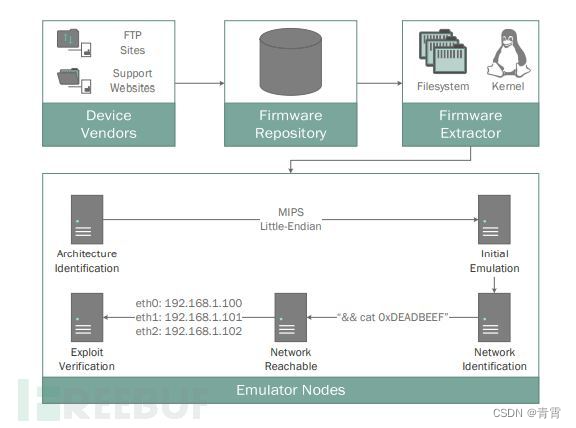
Firmadyne模块如下图所示:
其运行流程是:
通过网络途径获取固件(ARM/MIPS),并对固件解包;
利用定制动态链接库完成库函数劫持以完成NVRAM设备调用;
利用定制内核完成系统启动、网络探测、虚拟硬件和网络构建;
调用QEMU仿真系统
二、用法
2.1. 分析netgear防火墙
2.1.1. 固件自动提取与虚拟化运行
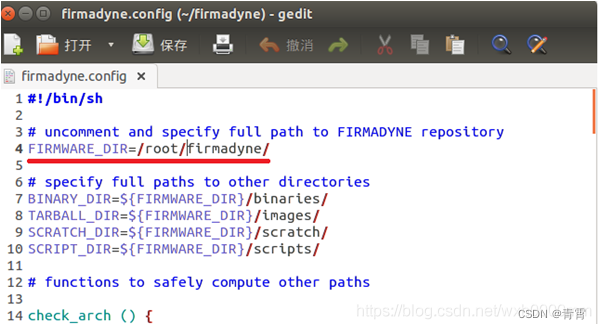
1、 在firemadyne目录修改firmadyne.config中的FIRMWARE_DIR为当前目录
2、下载 firmware 固件镜像
如:Netgear WNAP320 v2.0.3.
3、使用extractor提取filesystem
- nk:no kernel,不提取内核;
- np:no parallel operation,没有并行操作;
- sql:将镜像信息表存储到数据库127 .0.0.1 ;
- b: with the Netgear brand () ;
Images:存储压缩文件在images .
$ ./sources/extractor/extractor.py -b Netgear -sql 127.0.0.1 -np -nk "WNAP320 Firmware Version 2.0.3.zip" images
$ ./sources/extractor/extractor.py -b Netgear -sql 127.0.0.1 -np -nk "WNAP320 Firmware Version 2.0.3.zip" images
>> Database Image ID: 1
/root/firmadyne/WNAP320 Firmware Version2.0.3.zip
>> MD5:51eddc7046d77a752ca4b39fbda50aff
>> Tag: 1
>> Temp: /tmp/tmp0IdyGR
>> Status: Kernel: True, Rootfs:False, Do_Kernel: False, Do_Rootfs: True
>>>> Zip archive data, at leastv2.0 to extract, compressed size: 1197, uncompressed size: 2667, name:ReleaseNotes_WNAP320_fw_2.0.3.HTML
>> Recursing into archive ...
/tmp/tmp0IdyGR/_WNAP320 Firmware Version2.0.3.zip.extracted/WNAP320_V2.0.3_firmware.tar
>>MD5: 6b66d0c845ea6f086e0424158d8e5f26
>>Tag: 1
>>Temp: /tmp/tmpzzJmsI
>>Status: Kernel: True, Rootfs: False, Do_Kernel: False, Do_Rootfs: True
>>>>POSIX tar archive (GNU), owner user name: "gz.uImage"
>>Recursing into archive ...
/tmp/tmpzzJmsI/_WNAP320_V2.0.3_firmware.tar.extracted/kernel.md5
>>MD5: 0e15e5398024c854756d3e5f7bc78877
>>Skipping: text/plain...
/tmp/tmpzzJmsI/_WNAP320_V2.0.3_firmware.tar.extracted/root_fs.md5
>>MD5: b43dc86ce23660652d37d97651ba1c77
>>Skipping: text/plain...
/tmp/tmpzzJmsI/_WNAP320_V2.0.3_firmware.tar.extracted/rootfs.squashfs
>>MD5: 7ce95b252346d2486d55866a1a9782be
>>Tag: 1
>>Temp: /tmp/tmp16WDxR
>>Status: Kernel: True, Rootfs: False, Do_Kernel: False, Do_Rootfs: True
>>Recursing into archive ...
>>>>Squashfs filesystem, big endian, lzma signature, version 3.1, size: 4433988bytes, 1247 inodes, blocksize: 65536 bytes, created: 2011-06-23 10:46:19
>>>>Found Linux filesystem in/tmp/tmp16WDxR/_rootfs.squashfs.extracted/squashfs-root!
>>Skipping: completed!
>>Cleaning up /tmp/tmp16WDxR...
>>Skipping: completed!
>>Cleaning up /tmp/tmpzzJmsI...
>> Skipping: completed!
>> Cleaning up /tmp/tmp0IdyGR...
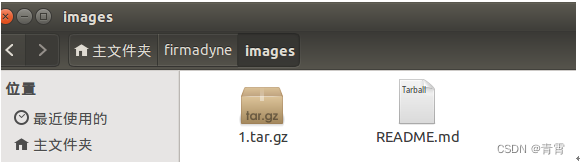
提取后文件如下:
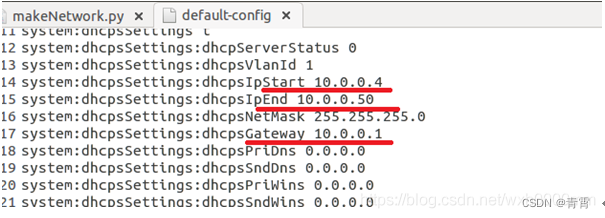
如果 想修改默认IP地址就修改1.tar.gz中的default-config文件中的默认ip address及网关等配置:
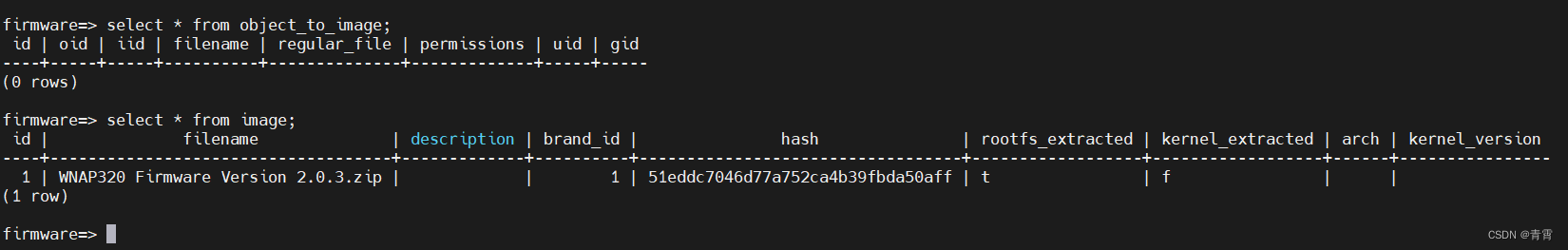
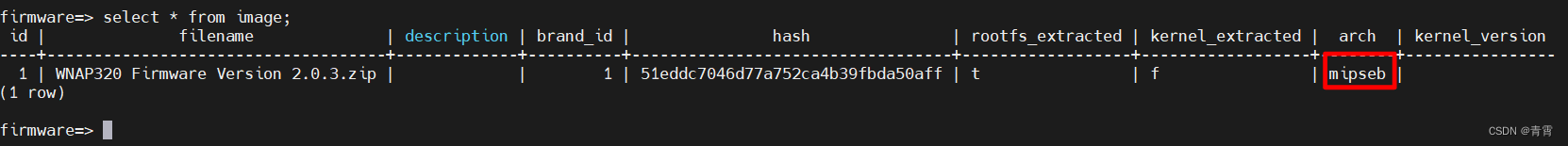
此时数据库:
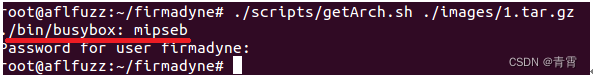
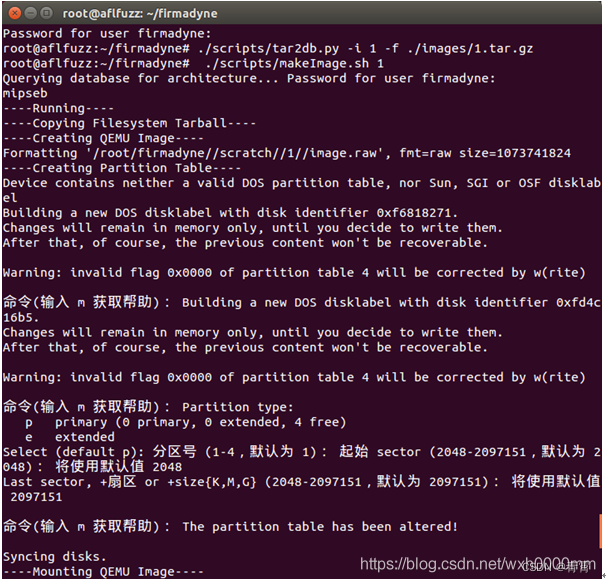
4、 识别固件的架构 并将结果存储在数据库的表中
识别防火墙1.tar.gz文件架构,并存储结果到数据库
./scripts/getArch.sh ./images/1.tar.gz
此时数据库:
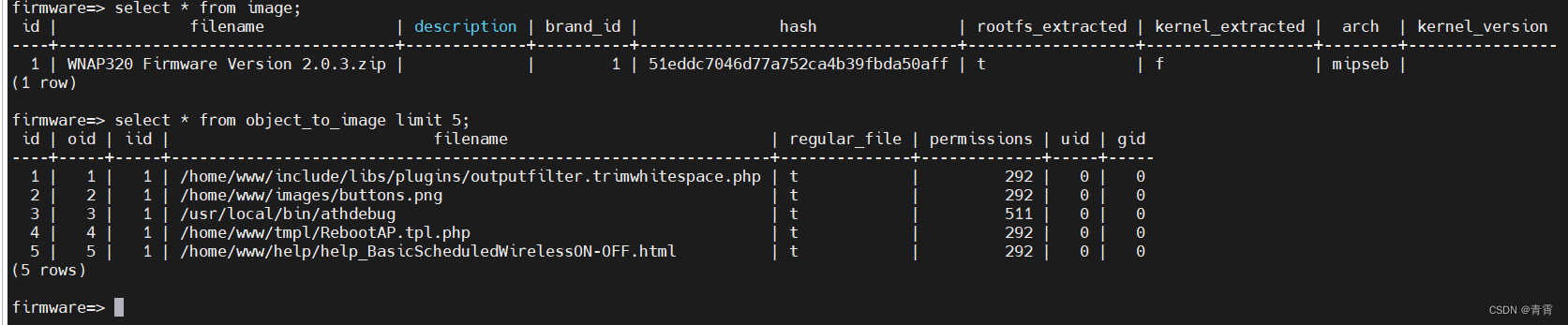
5、装载固件文件系统内容,存储对象到表 object_to_image
./scripts/tar2db.py -i 1 -f./images/1.tar.gz
此时数据库表object_to_image有数据:
7、 指定固件的网络配置并将信息记录到./scratch/1/qemu.initial.serial.log
./scripts/inferNetwork.sh 1
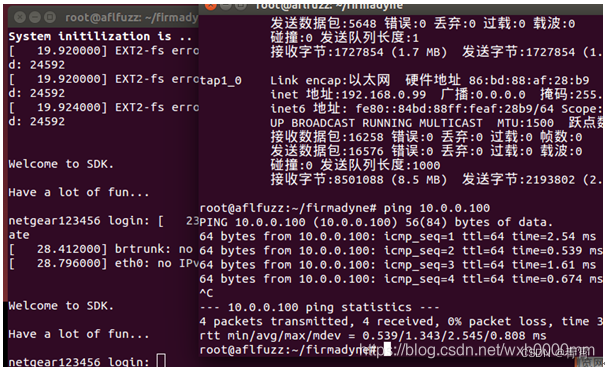
8、 使用指定的网络配置模拟运行防火墙
这将通过产生TAP设备增加route修改主机系统配置
./scratch/1/run.sh
输入 root/password,进入固件的终端shell。
web登录:admin/password
系统已经运行,属主机可以访问,系统信息被记录到 ./scratch/1/qemu.final.serial.log.
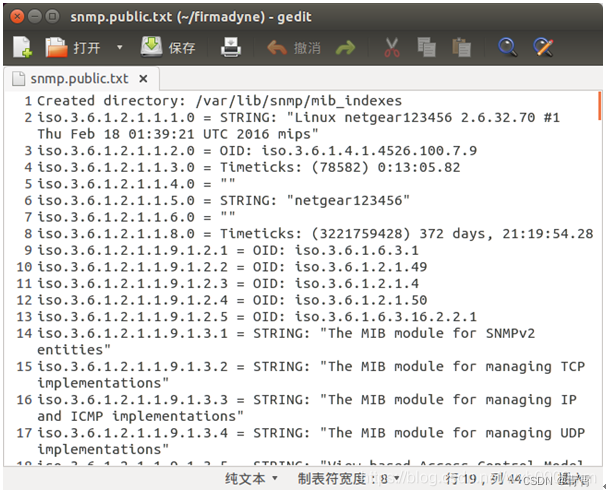
9、通过snmp脚本探测防火墙信息
./analyses/snmpwalk.sh 10.0.0.100
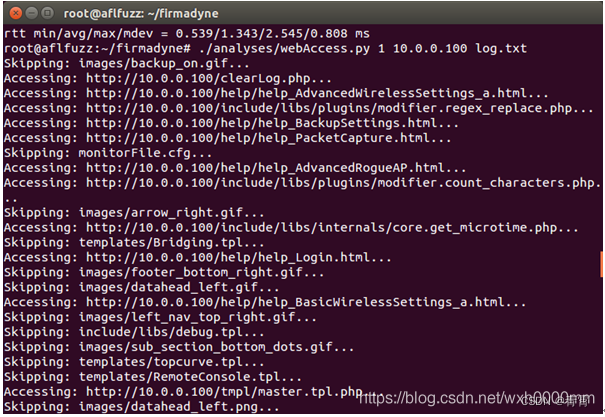
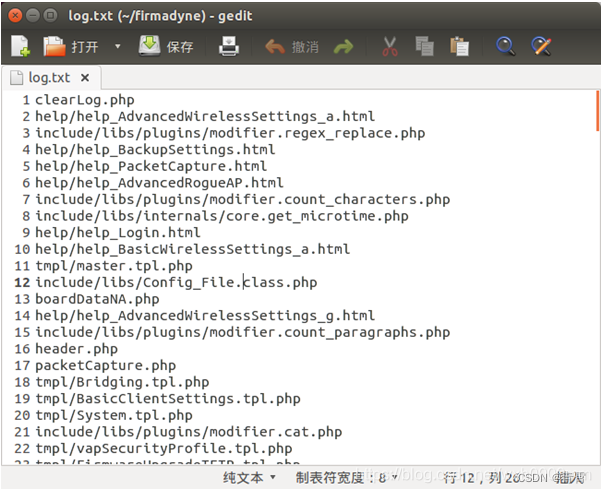
10、 测试防火墙web接口
./analyses/webAccess.py 1 10.0.0.100 log.txt
可访问目录会存储在log.txt文件中
2.1.2. 使用nmap扫描firmadyne虚拟环境运行的防火墙
root@aflfuzz:~/firmadyne# nmap -O -sV 10.0.0.100
Starting Nmap 7.40SVN ( https://nmap.org )at 2017-04-20 11:13 CST
Nmap scan report for localhost (10.0.0.100)
Host is up (0.0011s latency).
Not shown: 997 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh Dropbear sshd 0.51 (protocol 2.0)
80/tcp open http lighttpd 1.4.18
443/tcp open ssl/http lighttpd 1.4.18
MAC Address: 52:54:00:12:34:56 (QEMUvirtual NIC)
Device type: general purpose
Running: Linux 2.6.X
OS CPE: cpe:/o:linux:linux_kernel:2.6.32
OS details: Linux 2.6.32
Network Distance: 1 hop
Service Info: OS: Linux; CPE:cpe:/o:linux:linux_kernel
OS and Service detection performed. Pleasereport any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scannedin 68.30 seconds
2.1.3. 使用nmap vuln脚本探测防火墙漏洞
root@aflfuzz:~/firmadyne# nmap--script=vuln -O -sV 10.0.0.100
Starting Nmap 7.40SVN ( https://nmap.org )at 2017-04-20 11:22 CST
Pre-scan script results:
| broadcast-avahi-dos:
| Discovered hosts:
| 224.0.0.251
| After NULL UDP avahi packet DoS (CVE-2011-1002).
|_ Hosts are all up (not vulnerable).
Nmap scan report for localhost (10.0.0.100)
Host is up (0.0014s latency).
Not shown: 997 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh Dropbear sshd 0.51 (protocol 2.0)
80/tcp open http lighttpd 1.4.18
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
|_http-csrf: Couldn't find any CSRFvulnerabilities.
|_http-dombased-xss: Couldn't find any DOMbased XSS.
| http-enum:
|_ /test.php: Test page
|_http-phpself-xss: ERROR: Script executionfailed (use -d to debug)
|_http-server-header: lighttpd/1.4.18
| http-slowloris-check:
| VULNERABLE:
| Slowloris DOS attack
| State: LIKELY VULNERABLE
| IDs: CVE:CVE-2007-6750
| Slowloris tries to keep many connections to the target web server openand hold
| them open as long as possible. Itaccomplishes this by opening connections to
| the target web server and sending a partial request. By doing so, itstarves
| the http server's resources causing Denial Of Service.
|
| Disclosure date: 2009-09-17
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2007-6750
|_ http://ha.ckers.org/slowloris/
|_http-stored-xss: Couldn't find any storedXSS vulnerabilities.
443/tcp open ssl/http lighttpd 1.4.18
|_http-aspnet-debug: ERROR: Scriptexecution failed (use -d to debug)
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
|_http-csrf: Couldn't find any CSRFvulnerabilities.
|_http-dombased-xss: Couldn't find any DOMbased XSS.
| http-enum:
|_ /test.php: Test page
|_http-phpself-xss: ERROR: Script executionfailed (use -d to debug)
|_http-server-header: lighttpd/1.4.18
| http-slowloris-check:
| VULNERABLE:
| Slowloris DOS attack
| State: LIKELY VULNERABLE
| IDs: CVE:CVE-2007-6750
| Slowloris tries to keep many connections to the target web server openand hold
| them open as long as possible. Itaccomplishes this by opening connections to
| the target web server and sending a partial request. By doing so, itstarves
| the http server's resources causing Denial Of Service.
|
| Disclosure date: 2009-09-17
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2007-6750
|_ http://ha.ckers.org/slowloris/
|_http-stored-xss: Couldn't find any storedXSS vulnerabilities.
| ssl-ccs-injection:
| VULNERABLE:
| SSL/TLS MITM vulnerability (CCS Injection)
| State: VULNERABLE
| Risk factor: High
| OpenSSL before 0.9.8za, 1.0.0 before 1.0.0m, and 1.0.1 before 1.0.1h
| does not properly restrict processing of ChangeCipherSpec messages,
| which allows man-in-the-middle attackers to trigger use of a zero
| length master key in certain OpenSSL-to-OpenSSL communications, and
| consequently hijack sessions or obtain sensitive information, via
| a crafted TLS handshake, aka the "CCS Injection"vulnerability.
|
| References:
| http://www.openssl.org/news/secadv_20140605.txt
| http://www.cvedetails.com/cve/2014-0224
|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0224
| ssl-poodle:
| VULNERABLE:
| SSL POODLE information leak
| State: VULNERABLE
| IDs: CVE:CVE-2014-3566 OSVDB:113251
| The SSL protocol 3.0, as used in OpenSSL through 1.0.1i and other
| products, uses nondeterministic CBC padding, which makes it easier
| for man-in-the-middle attackers to obtain cleartext data via a
| padding-oracle attack, aka the "POODLE" issue.
| Disclosure date: 2014-10-14
| Check results:
| TLS_RSA_WITH_AES_128_CBC_SHA
| References:
| https://www.openssl.org/~bodo/ssl-poodle.pdf
| https://www.imperialviolet.org/2014/10/14/poodle.html
| http://osvdb.org/113251
|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-3566
| sslv2-drown:
| ciphers:
| SSL2_RC2_128_CBC_WITH_MD5
| SSL2_DES_64_CBC_WITH_MD5
| SSL2_DES_192_EDE3_CBC_WITH_MD5
| SSL2_RC4_128_WITH_MD5
| SSL2_RC2_128_CBC_EXPORT40_WITH_MD5
| SSL2_RC4_128_EXPORT40_WITH_MD5
| vulns:
| CVE-2016-0703:
| title: OpenSSL: Divide-and-conquer session key recovery in SSLv2
| state: VULNERABLE
| ids:
| CVE:CVE-2016-0703
| description:
| The get_client_master_keyfunction in s2_srvr.c in the SSLv2 implementation in
| OpenSSL before 0.9.8zf, 1.0.0 before 1.0.0r, 1.0.1 before 1.0.1m, and1.0.2 before
| 1.0.2a accepts a nonzero CLIENT-MASTER-KEY CLEAR-KEY-LENGTH value for anarbitrary
| cipher, which allows man-in-the-middle attackers to determine theMASTER-KEY value
| and decrypt TLS ciphertext data by leveraging a Bleichenbacher RSApadding oracle, a
| related issue to CVE-2016-0800.
|
| refs:
| https://www.openssl.org/news/secadv/20160301.txt
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-0703
| CVE-2016-0800:
| title: OpenSSL: Cross-protocol attack on TLS using SSLv2 (DROWN)
| state: VULNERABLE
| ids:
| CVE:CVE-2016-0800
| description:
| The SSLv2 protocol, as used inOpenSSL before 1.0.1s and 1.0.2 before 1.0.2g and
| other products, requires a server to send a ServerVerify message beforeestablishing
| that a client possesses certain plaintext RSA data, which makes iteasier for remote
| attackers to decrypt TLS ciphertext data by leveraging a BleichenbacherRSA padding
| oracle, aka a "DROWN" attack.
|
| refs:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-0800
|_ https://www.openssl.org/news/secadv/20160301.txt
MAC Address: 52:54:00:12:34:56 (QEMUvirtual NIC)
Device type: general purpose
Running: Linux 2.6.X
OS CPE: cpe:/o:linux:linux_kernel:2.6.32
OS details: Linux 2.6.32
Network Distance: 1 hop
Service Info: OS: Linux; CPE:cpe:/o:linux:linux_kernel
OS and Service detection performed. Pleasereport any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scannedin 192.14 seconds
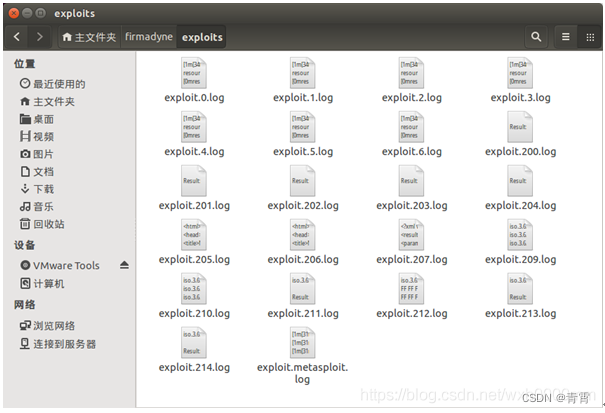
2.1.4. firmadyne对防火墙使用msf进行渗透
runExploits .py会自动使用metasploit中存在的路由器的攻击脚本进行自动攻击,执行结果会存储在exploits目录
root@aflfuzz:~/firmadyne# chmod +x analyses/*.py
root@aflfuzz:~/firmadyne# mkdir exploits
root@aflfuzz:~/firmadyne#./analyses/runExploits.py -t 192.168.0.100 -o exploits/exploit -e x # 需要 Metasploit 框架
默认控制台应自动连接到终端。 为了简化firmware的使用, 以root登录,密码是password ,删除 /etc/securetty。 使用下面的命令挂载或卸载fireware. 执行这两命令前确保模拟fireware未运行 。
sudo./scripts/mount.sh 1
sudo ./scripts/umount.sh 1
三、参考
推荐本站淘宝优惠价购买喜欢的宝贝:

本文链接:https://hqyman.cn/post/4813.html 非本站原创文章欢迎转载,原创文章需保留本站地址!
打赏

微信支付宝扫一扫,打赏作者吧~
休息一下~~





 微信支付宝扫一扫,打赏作者吧~
微信支付宝扫一扫,打赏作者吧~