libreswan + h3c建立ipsec 实现两idc内网网段互通
一、 环境介绍
上节中,我们介绍了使用两台libreswan实现两idc内网互通,今天我们看下如何使用libreswan和网络防火墙实现两idc互通。网络设备我们使用的是H3C的 F1000-AK125 防火墙
环境:
idc-重庆区域:
内网网段: 172.16.30.0/24
公网ip: 192.191.91.71 (公网ip修改)
内网ip: 172.16.30.15
主机版本: centos7
idc-test区域:
内网网段: 10.40.0.0/16
公网ip: 192.131.93.150 (公网ip修改)
内网ip: H3C
主机版本: F1000-AK125
架构图:

二、软件安装:
3.1 libreswan下载
centos 系统yum仓库中提供了libreswan的包,最新版本的rpm与设备存在兼容性问题。我们卸载新版本,使用yum安装
3.2 libreswan 安装
# rpm -ev libreswan # yum install -y libreswan [root@VM_0_13_centos ipsec.d]# yum info libreswan Loaded plugins: fastestmirror, langpacks Repository epel is listed more than once in the configuration Loading mirror speeds from cached hostfile Installed Packages Name : libreswan Arch : x86_64 Version : 3.25 Release : 8.1.el7_7 Size : 4.7 M Repo : installed From repo : updates Summary : IPsec implementation with IKEv1 and IKEv2 keying protocols URL : https://libreswan.org/ License : GPLv2 Description : Libreswan is a free implementation of IPsec & IKE for Linux. IPsec is : the Internet Protocol Security and uses strong cryptography to provide : both authentication and encryption services. These services allow you : to build secure tunnels through untrusted networks. Everything passing : through the untrusted net is encrypted by the ipsec gateway machine and : decrypted by the gateway at the other end of the tunnel. The resulting : tunnel is a virtual private network or VPN. : : This package contains the daemons and userland tools for setting up : Libreswan. It supports the NETKEY/XFRM IPsec kernel stack that exists : in the default Linux kernel. : : Libreswan also supports IKEv2 (RFC-7296) and Secure Labeling : : Libreswan is based on Openswan-2.6.38 which in turn is based on FreeS/WAN-2.04
三、 新建 ipsec 连接
3.1 创建连接配置:
vim /etc/ipsec.d/cq-to-test.conf conn test-vm-test ### phase 1 ### # 指定认证类型预共享秘钥 authby=secret # 指定ike算法为3des-sha1,非对称算法为dh24 (根据网络设备和libreswan支持的算法来定) ike=3des-sha1;dh24 # 指定ike keyexchange=ike ### phase 2 ### phase2=esp phase2alg=3des-sha1 # 指定是否压缩 compress=no # 指定是否加密 pfs=yes # 指定连接添加类型。start 为开机自启,add为添加 不主动连接 auto=start # 指定模式类型为隧道模式|传输模式 type=tunnel left=172.30.0.15 leftsubnet=172.30.0.0/24 leftid=192.191.91.71 leftnexthop=%defaultroute right=192.131.93.150 rightsubnet=10.40.0.0/16 rightid=192.131.93.150
3.2 重启 ipsec 服务
systemctl restart ipsec
四、配置 H3C 网络设备
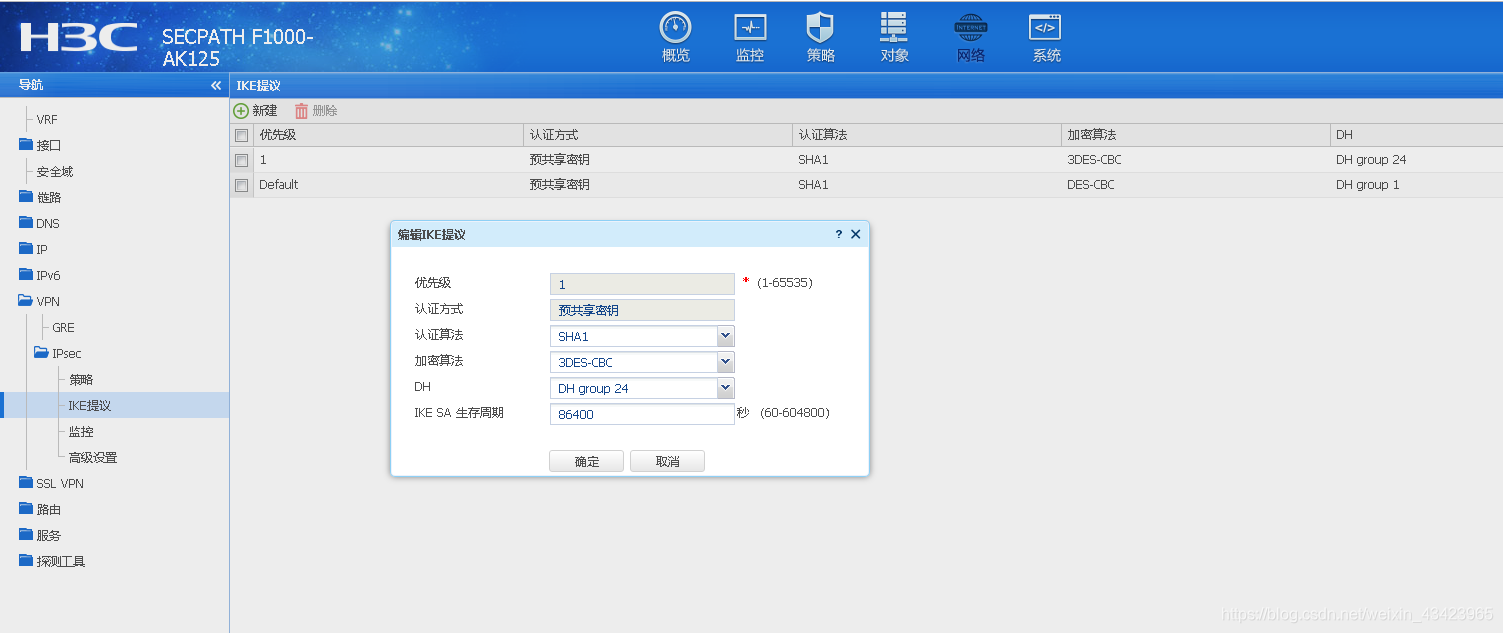
4.1 配置 ike 提议
根据libeswan中的配置,进行配置
4.2 新增ipse策略
指定模式 主动模式,对端ip地址,预共享秘钥,第二阶段的加密算法等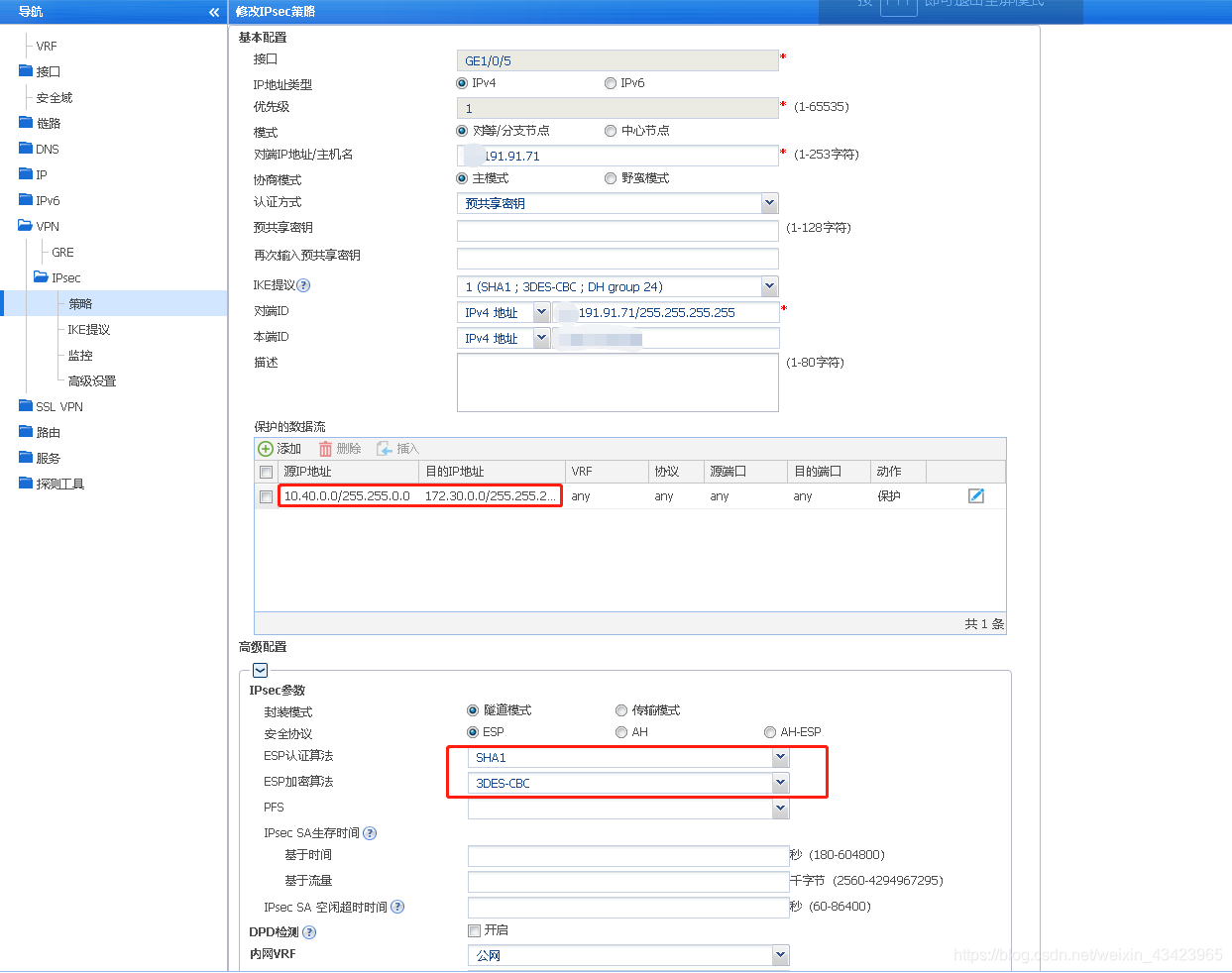
4.3 测试h3c设备的udp端口
[root@VM_0_15_centos ipsec.d]# nmap -sU 192.131.93.150 -p 4500,500 -Pn Starting Nmap 6.40 ( http://nmap.org ) at 2020-03-25 10:16 CST Nmap scan report for 192.131.93.150 Host is up (0.030s latency). PORT STATE SERVICE 500/udp open isakmp 4500/udp open|filtered nat-t-ike Nmap done: 1 IP address (1 host up) scanned in 3.77 seconds
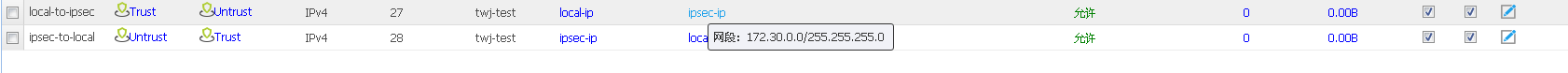
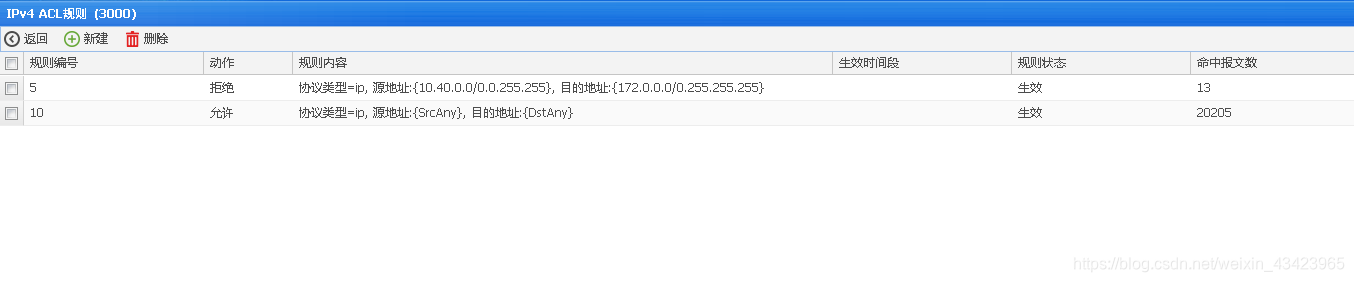
4.4 配置安全策略,开放两idc内部流量
五、 查看日志,建立ipsec隧道
5.1 查看日志 隧道建立情况
# 查看日志 隧道建立情况
[root@VM_0_15_centos ipsec.d]# ipsec auto --status
000 using kernel interface: netkey
000 interface lo/lo 127.0.0.1@4500
000 interface lo/lo 127.0.0.1@500
000 interface eth0/eth0 172.30.0.15@4500
000 interface eth0/eth0 172.30.0.15@500
000 interface tun0/tun0 10.8.0.1@4500
000 interface tun0/tun0 10.8.0.1@500
000
000
000 fips mode=disabled;
000 SElinux=disabled
000 seccomp=disabled
000
000 config setup options:
000
000 configdir=/etc, configfile=/etc/ipsec.conf, secrets=/etc/ipsec.secrets, ipsecdir=/etc/ipsec.d
000 nssdir=/etc/ipsec.d, dumpdir=/run/pluto, statsbin=unset
000 dnssec-rootkey-file=/var/lib/unbound/root.key, dnssec-trusted=<unset>
000 sbindir=/usr/sbin, libexecdir=/usr/libexec/ipsec
000 pluto_version=3.25, pluto_vendorid=OE-Libreswan-3.25
000 nhelpers=-1, uniqueids=yes, dnssec-enable=yes, perpeerlog=no, logappend=yes, logip=yes, shuntlifetime=900s, xfrmlifetime=300s
000 ddos-cookies-threshold=50000, ddos-max-halfopen=25000, ddos-mode=auto
000 ikeport=500, ikebuf=0, msg_errqueue=yes, strictcrlpolicy=no, crlcheckinterval=0, listen=<any>, nflog-all=0
000 ocsp-enable=no, ocsp-strict=no, ocsp-timeout=2, ocsp-uri=<unset>
000 ocsp-trust-name=<unset>
000 ocsp-cache-size=1000, ocsp-cache-min-age=3600, ocsp-cache-max-age=86400, ocsp-method=get
000 secctx-attr-type=32001
000 debug:
000
000 nat-traversal=yes, keep-alive=20, nat-ikeport=4500
000 virtual-private (%priv):
000 - allowed subnets: 10.0.0.0/8, 192.168.0.0/16, 172.16.0.0/12, 25.0.0.0/8, 100.64.0.0/10, fd00::/8, fe80::/10
000
000 ESP algorithms supported:
000
000 algorithm ESP encrypt: id=3, name=ESP_3DES, ivlen=8, keysizemin=192, keysizemax=192
000 algorithm ESP encrypt: id=6, name=ESP_CAST, ivlen=8, keysizemin=128, keysizemax=128
000 algorithm ESP encrypt: id=11, name=ESP_NULL, ivlen=0, keysizemin=0, keysizemax=0
000 algorithm ESP encrypt: id=12, name=ESP_AES, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=13, name=ESP_AES_CTR, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=14, name=ESP_AES_CCM_A, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=15, name=ESP_AES_CCM_B, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=16, name=ESP_AES_CCM_C, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=18, name=ESP_AES_GCM_A, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=19, name=ESP_AES_GCM_B, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=20, name=ESP_AES_GCM_C, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=22, name=ESP_CAMELLIA, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=23, name=ESP_NULL_AUTH_AES_GMAC, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=252, name=ESP_SERPENT, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=253, name=ESP_TWOFISH, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm AH/ESP auth: id=1, name=AUTH_ALGORITHM_HMAC_MD5, keysizemin=128, keysizemax=128
000 algorithm AH/ESP auth: id=2, name=AUTH_ALGORITHM_HMAC_SHA1, keysizemin=160, keysizemax=160
000 algorithm AH/ESP auth: id=5, name=AUTH_ALGORITHM_HMAC_SHA2_256, keysizemin=256, keysizemax=256
000 algorithm AH/ESP auth: id=6, name=AUTH_ALGORITHM_HMAC_SHA2_384, keysizemin=384, keysizemax=384
000 algorithm AH/ESP auth: id=7, name=AUTH_ALGORITHM_HMAC_SHA2_512, keysizemin=512, keysizemax=512
000 algorithm AH/ESP auth: id=8, name=AUTH_ALGORITHM_HMAC_RIPEMD, keysizemin=160, keysizemax=160
000 algorithm AH/ESP auth: id=9, name=AUTH_ALGORITHM_AES_XCBC, keysizemin=128, keysizemax=128
000 algorithm AH/ESP auth: id=250, name=AUTH_ALGORITHM_AES_CMAC_96, keysizemin=128, keysizemax=128
000 algorithm AH/ESP auth: id=251, name=AUTH_ALGORITHM_NULL_KAME, keysizemin=0, keysizemax=0
000
000 IKE algorithms supported:
000
000 algorithm IKE encrypt: v1id=5, v1name=OAKLEY_3DES_CBC, v2id=3, v2name=3DES, blocksize=8, keydeflen=192
000 algorithm IKE encrypt: v1id=8, v1name=OAKLEY_CAMELLIA_CBC, v2id=23, v2name=CAMELLIA_CBC, blocksize=16, keydeflen=128
000 algorithm IKE encrypt: v1id=-1, v1name=n/a, v2id=20, v2name=AES_GCM_C, blocksize=16, keydeflen=128
000 algorithm IKE encrypt: v1id=-1, v1name=n/a, v2id=19, v2name=AES_GCM_B, blocksize=16, keydeflen=128
000 algorithm IKE encrypt: v1id=-1, v1name=n/a, v2id=18, v2name=AES_GCM_A, blocksize=16, keydeflen=128
000 algorithm IKE encrypt: v1id=13, v1name=OAKLEY_AES_CTR, v2id=13, v2name=AES_CTR, blocksize=16, keydeflen=128
000 algorithm IKE encrypt: v1id=7, v1name=OAKLEY_AES_CBC, v2id=12, v2name=AES_CBC, blocksize=16, keydeflen=128
000 algorithm IKE encrypt: v1id=65004, v1name=OAKLEY_SERPENT_CBC, v2id=65004, v2name=SERPENT_CBC, blocksize=16, keydeflen=128
000 algorithm IKE encrypt: v1id=65005, v1name=OAKLEY_TWOFISH_CBC, v2id=65005, v2name=TWOFISH_CBC, blocksize=16, keydeflen=128
000 algorithm IKE encrypt: v1id=65289, v1name=OAKLEY_TWOFISH_CBC_SSH, v2id=65289, v2name=TWOFISH_CBC_SSH, blocksize=16, keydeflen=128
000 algorithm IKE PRF: name=HMAC_MD5, hashlen=16
000 algorithm IKE PRF: name=HMAC_SHA1, hashlen=20
000 algorithm IKE PRF: name=HMAC_SHA2_256, hashlen=32
000 algorithm IKE PRF: name=HMAC_SHA2_384, hashlen=48
000 algorithm IKE PRF: name=HMAC_SHA2_512, hashlen=64
000 algorithm IKE PRF: name=AES_XCBC, hashlen=16
000 algorithm IKE DH Key Exchange: name=MODP1024, bits=1024
000 algorithm IKE DH Key Exchange: name=MODP1536, bits=1536
000 algorithm IKE DH Key Exchange: name=MODP2048, bits=2048
000 algorithm IKE DH Key Exchange: name=MODP3072, bits=3072
000 algorithm IKE DH Key Exchange: name=MODP4096, bits=4096
000 algorithm IKE DH Key Exchange: name=MODP6144, bits=6144
000 algorithm IKE DH Key Exchange: name=MODP8192, bits=8192
000 algorithm IKE DH Key Exchange: name=DH19, bits=512
000 algorithm IKE DH Key Exchange: name=DH20, bits=768
000 algorithm IKE DH Key Exchange: name=DH21, bits=1056
000 algorithm IKE DH Key Exchange: name=DH22, bits=1024
000 algorithm IKE DH Key Exchange: name=DH23, bits=2048
000 algorithm IKE DH Key Exchange: name=DH24, bits=2048
000
000 stats db_ops: {curr_cnt, total_cnt, maxsz} :context={0,10,64} trans={0,10,6936} attrs={0,10,4624}
000
000 Connection list:
000
000 "cq-to-test": 172.30.0.0/24===172.30.0.15<172.30.0.15>[94.191.91.71]---172.30.0.1...192.131.93.150<192.131.93.150>===10.40.0.0/16; erouted; eroute owner: #48
000 "cq-to-test": oriented; my_ip=unset; their_ip=unset; my_updown=ipsec _updown;
000 "cq-to-test": xauth us:none, xauth them:none, my_username=[any]; their_username=[any]
000 "cq-to-test": our auth:secret, their auth:secret
000 "cq-to-test": modecfg info: us:none, them:none, modecfg policy:push, dns:unset, domains:unset, banner:unset, cat:unset;
000 "cq-to-test": labeled_ipsec:no;
000 "cq-to-test": policy_label:unset;
000 "cq-to-test": ike_life: 3600s; ipsec_life: 28800s; replay_window: 32; rekey_margin: 540s; rekey_fuzz: 100%; keyingtries: 0;
000 "cq-to-test": retransmit-interval: 500ms; retransmit-timeout: 60s;
000 "cq-to-test": initial-contact:no; cisco-unity:no; fake-strongswan:no; send-vendorid:no; send-no-esp-tfc:no;
000 "cq-to-test": policy: PSK+ENCRYPT+TUNNEL+PFS+UP+IKEV1_ALLOW+IKEV2_ALLOW+SAREF_TRACK+IKE_FRAG_ALLOW+ESN_NO;
000 "cq-to-test": conn_prio: 24,16; interface: eth0; metric: 0; mtu: unset; sa_prio:auto; sa_tfc:none;
000 "cq-to-test": nflog-group: unset; mark: unset; vti-iface:unset; vti-routing:no; vti-shared:no; nic-offload:auto;
000 "cq-to-test": our idtype: ID_IPV4_ADDR; our id=94.191.91.71; their idtype: ID_IPV4_ADDR; their id=192.131.93.150
000 "cq-to-test": dpd: action:hold; delay:0; timeout:0; nat-t: encaps:auto; nat_keepalive:yes; ikev1_natt:both
000 "cq-to-test": newest ISAKMP SA: #50; newest IPsec SA: #48;
000 "cq-to-test": IKE algorithms: 3DES_CBC-HMAC_SHA1-DH24
000 "cq-to-test": IKE algorithm newest: 3DES_CBC_192-HMAC_SHA1-DH24
000 "cq-to-test": ESP algorithms: 3DES_CBC-HMAC_SHA1_96
000 "cq-to-test": ESP algorithm newest: 3DES_CBC_000-HMAC_SHA1_96; pfsgroup=<Phase1>
000 Total IPsec connections: loaded 2, active 2
000
000 State Information: DDoS cookies not required, Accepting new IKE connections
000 IKE SAs: total(3), half-open(0), open(0), authenticated(3), anonymous(0)
000 IPsec SAs: total(2), authenticated(2), anonymous(0)
000
000 #48: "cq-to-test":4500 STATE_QUICK_R2 (IPsec SA established); EVENT_SA_REPLACE in 27s; newest IPSEC; eroute owner; isakmp#47; idle; import:admin initiate
000 #48: "cq-to-test" esp.32ee2bd0@192.131.93.150 esp.f8e56fff@172.30.0.15 tun.0@192.131.93.150 tun.0@172.30.0.15 ref=0 refhim=0 Traffic: ESPin=137KB ESPout=517KB! ESPmax=1800B
000 #50: "cq-to-test":4500 STATE_MAIN_I4 (ISAKMP SA established); EVENT_SA_REPLACE in 2278s; newest ISAKMP; lastdpd=-1s(seq in:0 out:0); idle; import:admin initiate
000 Bare Shunt list:
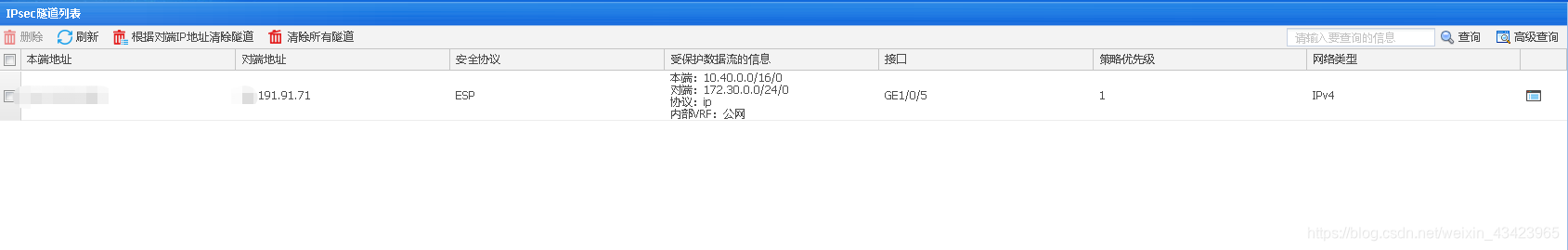
0005.2 查看防火墙隧道
5.3 测试连通性,发现内网不通
# ping 172.30.0.15 PING 172.30.0.15 (172.30.0.15) 56(84) bytes of data. ^
六、修改H3C网络策略,禁止两idc内网走路由策略(pat)

测试网络连接
# ifconfig ens192 ens192: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500 inet 10.40.11.161 netmask 255.255.255.0 broadcast 10.40.11.255 inet6 fe80::250:56ff:fe87:4c94 prefixlen 64 scopeid 0x20<link> ether 00:50:56:87:4c:94 txqueuelen 1000 (Ethernet) RX packets 72406265 bytes 9700278789 (9.0 GiB) RX errors 0 dropped 724 overruns 0 frame 0 TX packets 50762938 bytes 22251487246 (20.7 GiB) TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0 # ping 172.30.0.15 PING 172.30.0.15 (172.30.0.15) 56(84) bytes of data. 64 bytes from 172.30.0.15: icmp_seq=1 ttl=62 time=33.1 ms 64 bytes from 172.30.0.15: icmp_seq=2 ttl=62 time=33.0 ms 64 bytes from 172.30.0.15: icmp_seq=3 ttl=62 time=33.0 ms # tcpdump -vvv -n -i ens192 -p icpm 10.40.11.161 > 172.30.0.15: ICMP echo request, id 5020, seq 79, length 64 09:45:36.340985 IP (tos 0x0, ttl 62, id 3624, offset 0, flags [none], proto ICMP (1), length 84) 172.30.0.15 > 10.40.11.161: ICMP echo reply, id 5020, seq 79, length 64 09:45:37.310072 IP (tos 0x0, ttl 64, id 55095, offset 0, flags [DF], proto ICMP (1), length 84) 10.40.11.161 > 172.30.0.15: ICMP echo request, id 5020, seq 80, length 64 09:45:37.342989 IP (tos 0x0, ttl 62, id 4258, offset 0, flags [none], proto ICMP (1), length 84) 172.30.0.15 > 10.40.11.161: ICMP echo reply, id 5020, seq 80, length 64 09:45:38.312063 IP (tos 0x0, ttl 64, id 55419, offset 0, flags [DF], proto ICMP (1), length 84) 10.40.11.161 > 172.30.0.15: ICMP echo request, id 5020, seq 81, length 64 09:45:38.346113 IP (tos 0x0, ttl 62, id 4892, offset 0, flags [none], proto ICMP (1), length 84) 172.30.0.15 > 10.40.11.161: ICMP echo reply, id 5020, seq 81, length 64
45:38.312063 IP (tos 0x0, ttl 64, id 55419, offset 0, flags [DF], proto ICMP (1), length 84)
10.40.11.161 > 172.30.0.15: ICMP echo request, id 5020, seq 81, length 64
09:45:38.346113 IP (tos 0x0, ttl 62, id 4892, offset 0, flags [none], proto ICMP (1), length 84)
172.30.0.15 > 10.40.11.161: ICMP echo reply, id 5020, seq 81, length 64
推荐本站淘宝优惠价购买喜欢的宝贝:
本文链接:https://hqyman.cn/post/4898.html 非本站原创文章欢迎转载,原创文章需保留本站地址!
 微信支付宝扫一扫,打赏作者吧~
微信支付宝扫一扫,打赏作者吧~休息一下~~


