公网 to Home方案
Home 电信宽带有 public ip,用NAS虚拟出一个Centos7服务器
之前使用L2TP Over IPsec效果始终不太如人意,逐当作备用方案
安装依赖
mv /etc/yum.repos.d/CentOS-Base.repo /etc/yum.repos.d/CentOS-Base.repo.backup
wget -O /etc/yum.repos.d/CentOS-Base.repo http://mirrors.aliyun.com/repo/Centos-7.repo
yum clean all
yum makecach
yum remove epel-release -y# 如果是纯净系统安装可跳过上面yum install update epel-release -y
yum install ocserv -y创建一个临时目录
mkdir anyconnect && cd anyconnect生成证书
创建自签名CA证书,如果有SSL证书,以及不打算用证书认证,可以跳过
# Create CA certificate
erttool --generate-privkey --outfile ca-key.pem
cat >ca.tmpl <<EOF
cn = "Ocserv Server"
organization = "Super Big"
serial = 1
expiration_days = 3650
ca
signing_key
cert_signing_key
crl_signing_key
EOF
certtool --generate-self-signed --load-privkey ca-key.pem \
--template ca.tmpl --outfile ca-cert.pem
cp ca-cert.pem /etc/pki/ocserv/cacerts创建服务证书以及key
certtool --generate-privkey --outfile server-key.pem
cat >server.tmpl <<EOF
cn = "Ocserv Server"
organization = "Super Big"
serial = 2
expiration_days = 3650
encryption_key
signing_key
tls_www_server
EOF
certtool --generate-certificate --load-privkey server-key.pem \
--load-ca-certificate ca-cert.pem --load-ca-privkey ca-key.pem \
--template server.tmpl --outfile server-cert.pem
cp server-cert.pem /etc/pki/ocserv/public/server.crt
cp server-key.pem /etc/pki/ocserv/private/server.key创建一个生成用户证书的脚本,用于客户端认证
#!/bin/bash
USER=$1
CA_DIR=$2
SERIAL=`date +%s`
certtool --generate-privkey --outfile $USER-key.pem
cat << _EOF_ >user.tmpl
cn = "$USER"
unit = "users"
serial = "$SERIAL"
expiration_days = 9999
signing_key
tls_www_client
_EOF_
certtool --generate-certificate --load-privkey $USER-key.pem --load-ca-certificate $CA_DIR/ca-cert.pem --load-ca-privkey $CA_DIR/ca-key.pem --template user.tmpl --outfile $USER-cert.pem
openssl pkcs12 -export -inkey $USER-key.pem -in $USER-cert.pem -name "$USER VPN Client Cert" -certfile $CA_DIR/ca-cert.pem -out $USER.p12生成用户证书
mkdir user
cd user
./gen-client-cert.sh user user/
# 会要求输入两此证书密码配置文件
# 密码认证为先,并开启证书认证
auth = "plain[passwd=/etc/ocserv/ocpasswd]"
enable-auth = "certificate"
# 监听端口
tcp-port = 19999
udp-port = 19999
run-as-user = ocserv
run-as-group = ocserv
socket-file = ocserv.sock
chroot-dir = /var/lib/ocserv
max-clients = 10
max-same-clients = 10
rate-limit-ms = 100
keepalive = 300
dpd = 90
mobile-dpd = 300
switch-to-tcp-timeout = 25
# 我这里手动设置MTU 就关掉了
# 开启的话就是连接上了之后会测试MTU,然后会断开在重连一下
#try-mtu-discovery = true
# 如果有自己的证书,自行替换即可
ca-cert = /etc/pki/ocserv/cacerts/ca-cert.pem
server-cert = /etc/pki/ocserv/public/cert.crt
server-key = /etc/pki/ocserv/private/private.key
cert-user-oid = 2.5.4.3
tls-priorities = "NORMAL:%SERVER_PRECEDENCE:%COMPAT:-VERS-SSL3.0"
auth-timeout = 240
min-reauth-time = 300
max-ban-score = 50
ban-reset-time = 300
cookie-timeout = 86400
deny-roaming = false
rekey-time = 172800
rekey-method = ssl
use-occtl = true
device = vpns
# 这里可随意,当然如果你不用主机的防火墙 NAT的话,记得给子网写路由
default-domain = vpn.superbing.com
ipv4-network = 172.31.0.0/24
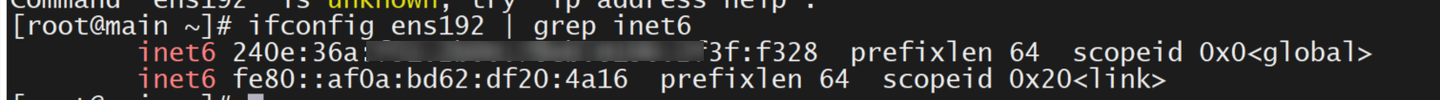
ipv6-network = 240e:36a:fcb:ea00::/64
# 小鱼1350不会分配v6地址
mtu = 1400
dns = 10.0.0.50
ping-leases = false
compression = true
predictable-ips = true
# 因为使用Cisco AnyConnect客户端 所以开启
cisco-client-compat = true
dtls-legacy = true主机开启NAT,防火墙
echo "net.ipv4.ip_forward = 1" >> /etc/sysctl.conf
sysctl -p /etc/sysctl.conf
#使用firewalledfirewall-cmd --permanent --add-port=59999/tcp
firewall-cmd --permanent --add-port=59999/udp
# 开启防火墙的地址伪装也就是NAT
firewall-cmd --permanent --add-masquerade
firewall-cmd --reload创建用户名密码
username ,for you need create username
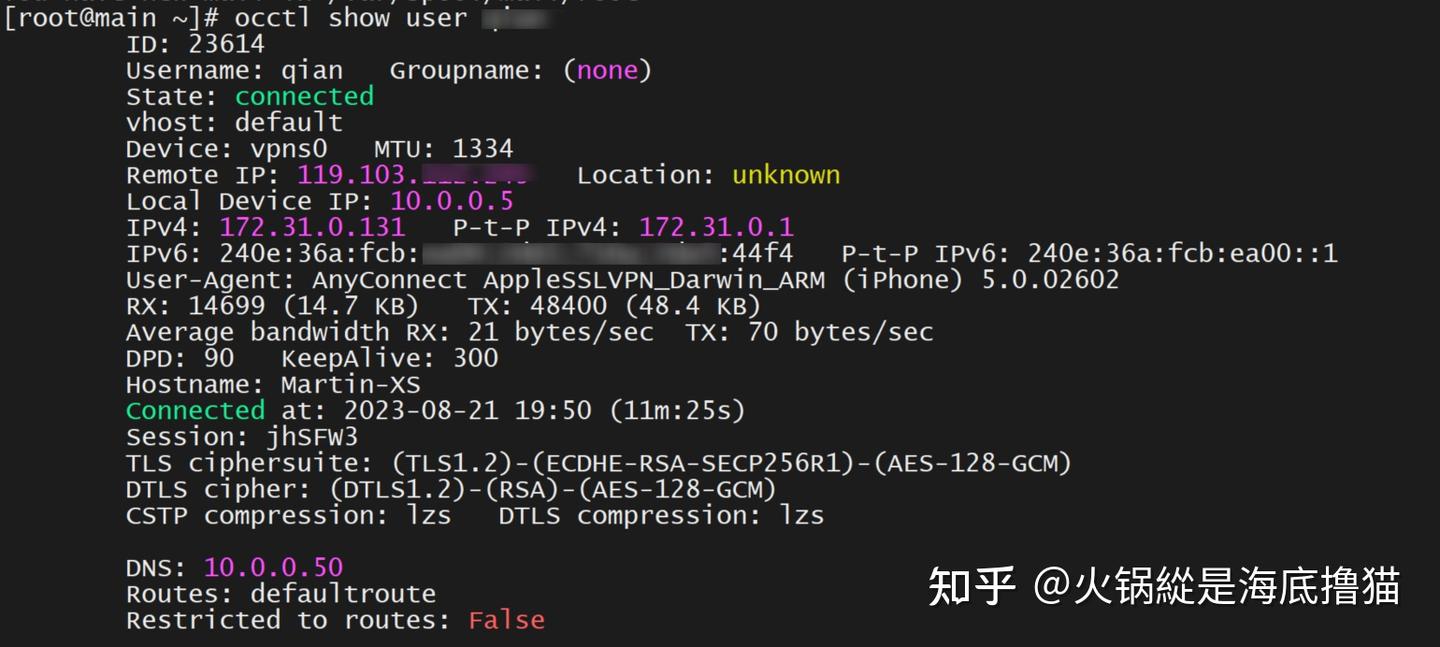
sudo ocpasswd -c /etc/ocserv/ocpasswd usernameOcctl 维护命令
occtl -n show status
occtl -n show users
occtl disconnect user 'username'
occtl disconnect id 'id_number'客户端
使用的Cisco AnyConnect ,iOS也有app
我是用的证书认证,可以不用输入密码,配合CLI写个脚本 (因为电脑要经常切换网络,有些静态有些动态)
@echo off
%1 mshta vbscript:CreateObject("Shell.Application").ShellExecute("cmd.exe","/c %~s0 ::","","runas",1)(window.close)&&exitecho "1,Home use static address"echo "2,use DHCP get address"echo "5,Connect to SSL VPN default route"echo "6,Connect to SSL VPN stub route"echo "8,Disconnect SSL VPN Connect"echo "9,Show SSL VPN Current status"echo set /p option="Please input you option: ":if %option%==1 (
netsh interface ipv4 set address name="Wi-Fi" source=static address=10.0.0.2 mask=255.255.255.0 gateway=10.0.0.1
netsh interface ipv4 set dnsservers "Wi-Fi" static 10.0.0.1 primary
taskkill /IM vpnui.exe /F
taskkill /IM outlook.exe /F cd "C:\Program Files (x86)\Cisco\Cisco AnyConnect Secure Mobility Client\" vpncli.exe disconnect ipconfig/flushdns) else if %option%==2 ( netsh interface ip set address name="Wi-Fi" source=dhcp netsh interface ip set dns name="Wi-Fi" source=dhcp ipconfig/flushdns timeout /nobreak /t 5 cd "C:\Program Files (x86)\Cisco\Cisco AnyConnect Secure Mobility Client\"
vpncli.exe connect https://vpn.superbig.com:59999
vpncli.exe state
ipconfig/flushdns) else if %option%==5 (
cd "C:\Program Files (x86)\Cisco\Cisco AnyConnect Secure Mobility Client\" vpncli.exe disconnect vpncli.exe connect https://vpn.superbig.com:59998 vpncli.exe stats ipconfig/flushdns) else if %option%==6 ( cd "C:\Program Files (x86)\Cisco\Cisco AnyConnect Secure Mobility Client\"
vpncli.exe disconnect
vpncli.exe connect https://vpn.superbig.com:59999
vpncli.exe stats
ipconfig/flushdns) else if %option%==8 (
cd "C:\Program Files (x86)\Cisco\Cisco AnyConnect Secure Mobility Client\" vpncli.exe disconnect ipconfig/flushdns ipconfig/all) else ( cd "C:\Program Files (x86)\Cisco\Cisco AnyConnect Secure Mobility Client\"
vpncli.exe state
vpncli.exe stats)pause测试v4连接VPN 获得双栈地址
可以看到通过IPv4 连接上的服务器
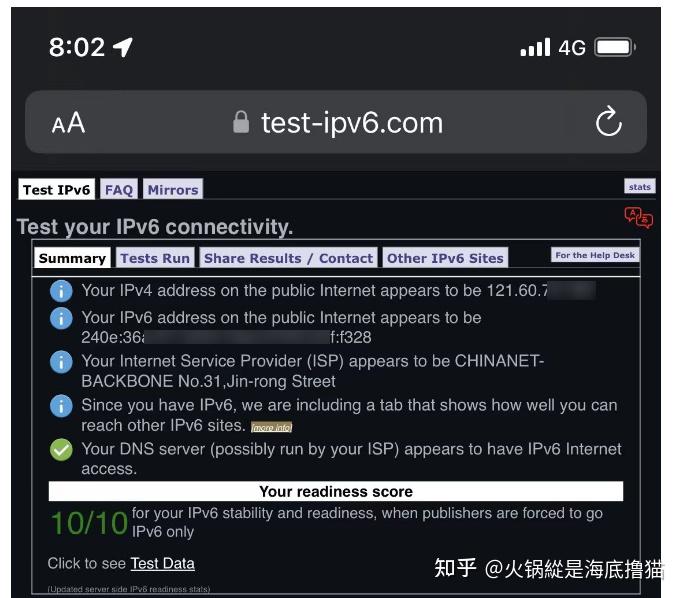
测试双栈网络正常!
推荐本站淘宝优惠价购买喜欢的宝贝:
以下内容需要兑换:本文链接:https://hqyman.cn/post/8647.html 非本站原创文章欢迎转载,原创文章需保留本站地址!
休息一下~~


 微信支付宝扫一扫,打赏作者吧~
微信支付宝扫一扫,打赏作者吧~